Azure AD Connection¶
Azure AD is the newer version of identity and access management created by Microsoft. It is an on-cloud version of its peer on-premises Active Directory. Azure AD is great at managing user access to cloud applications.
The Hire2Retire platform provides two connection types for Azure AD applications:
- Service Provider Application - In this option, you'll be require to sign-up and delegating the accesses to the RoboMQ application on your behalf
- Customer Owned Application - This option is recommended if you prefer employing your dedicated service account for automation purposes.
Service Provider Application¶
Azure AD application on hire2retire uses OAuth authorization. By linking your Azure AD account with hire2retire, you can authorise the RoboMQ application to have delegated access on your behalf, for which you will be provided with a consent window whenever new resource access permission is required by hire2retire. RoboMQ needs the following permissions on your account to provide a seamless integration experience:
| Scopes | Explanation |
|---|---|
| User.ReadWrite.All | Read and write all user's full profiles |
| Group.ReadWrite.All | Read and write all groups |
| Directory.AccessAsUser.All | Application requires this scope to reset their password. |
| offline_access | Maintain access to data you have given it access to. When a user approves the offline_access scope, your app can receive refresh tokens from the Microsoft identity platform token endpoint. Refresh tokens are long-lived. Your app can get new access tokens as older ones expire. |
Create a Connection¶
You need to have an Azure AD account before using Azure AD application on hire2retire.
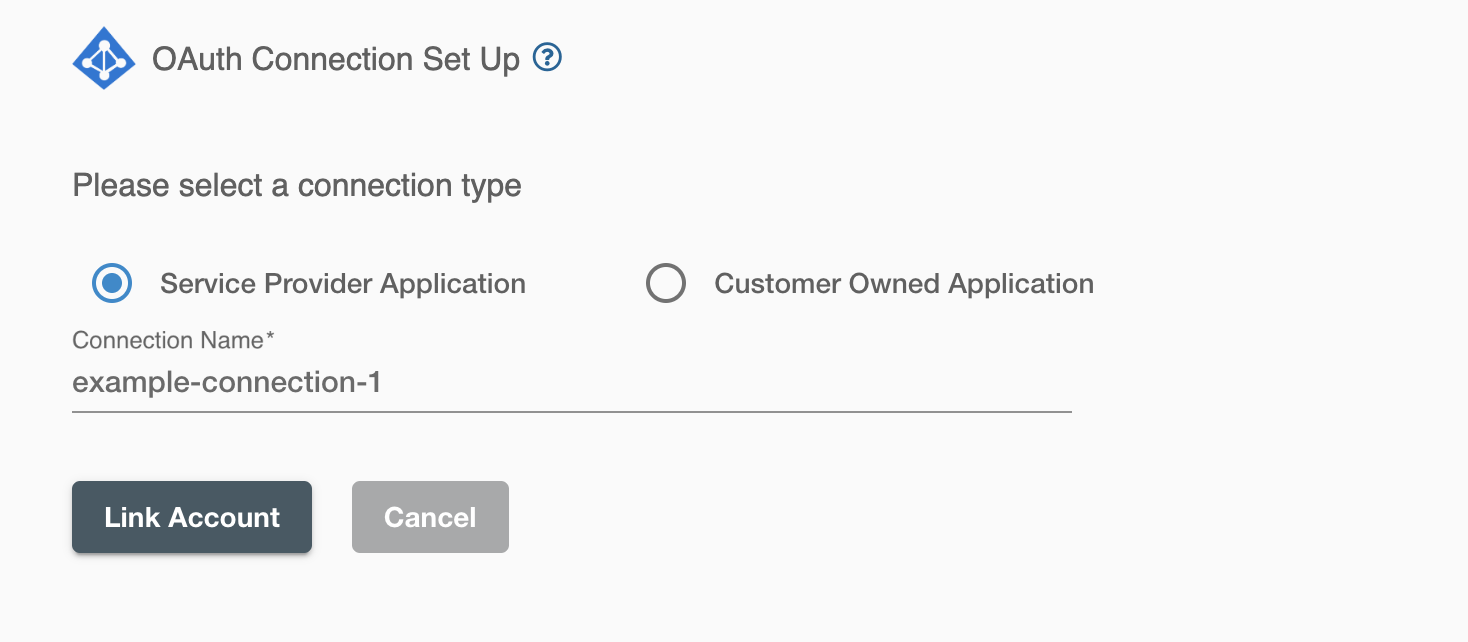
On clicking the 'Link Account' button, you will be redirected to Microsoft Account Authorization screen. and then enter the account details to use the Azure AD for this flow
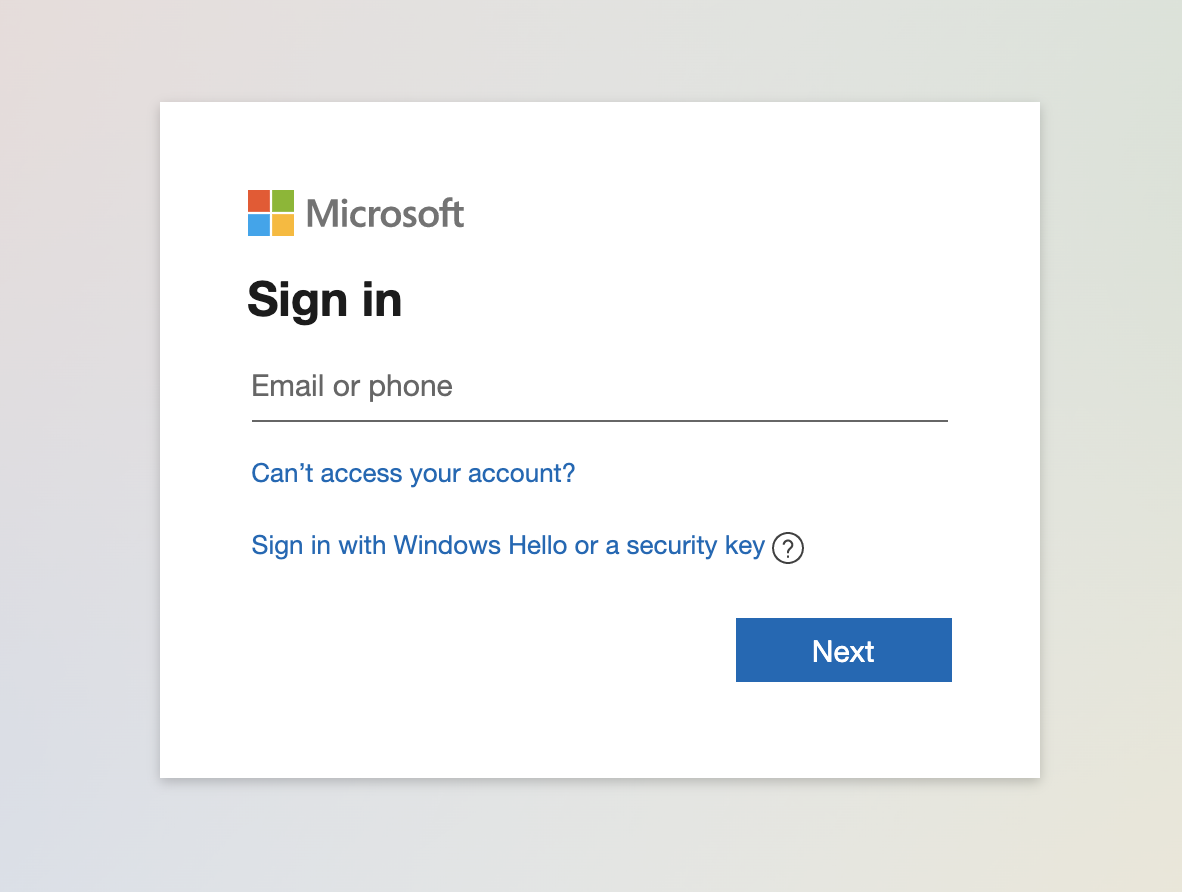
By allowing access, you are authorizing RoboMQ to access your AzureAD account and make changes based on changes in HR data.
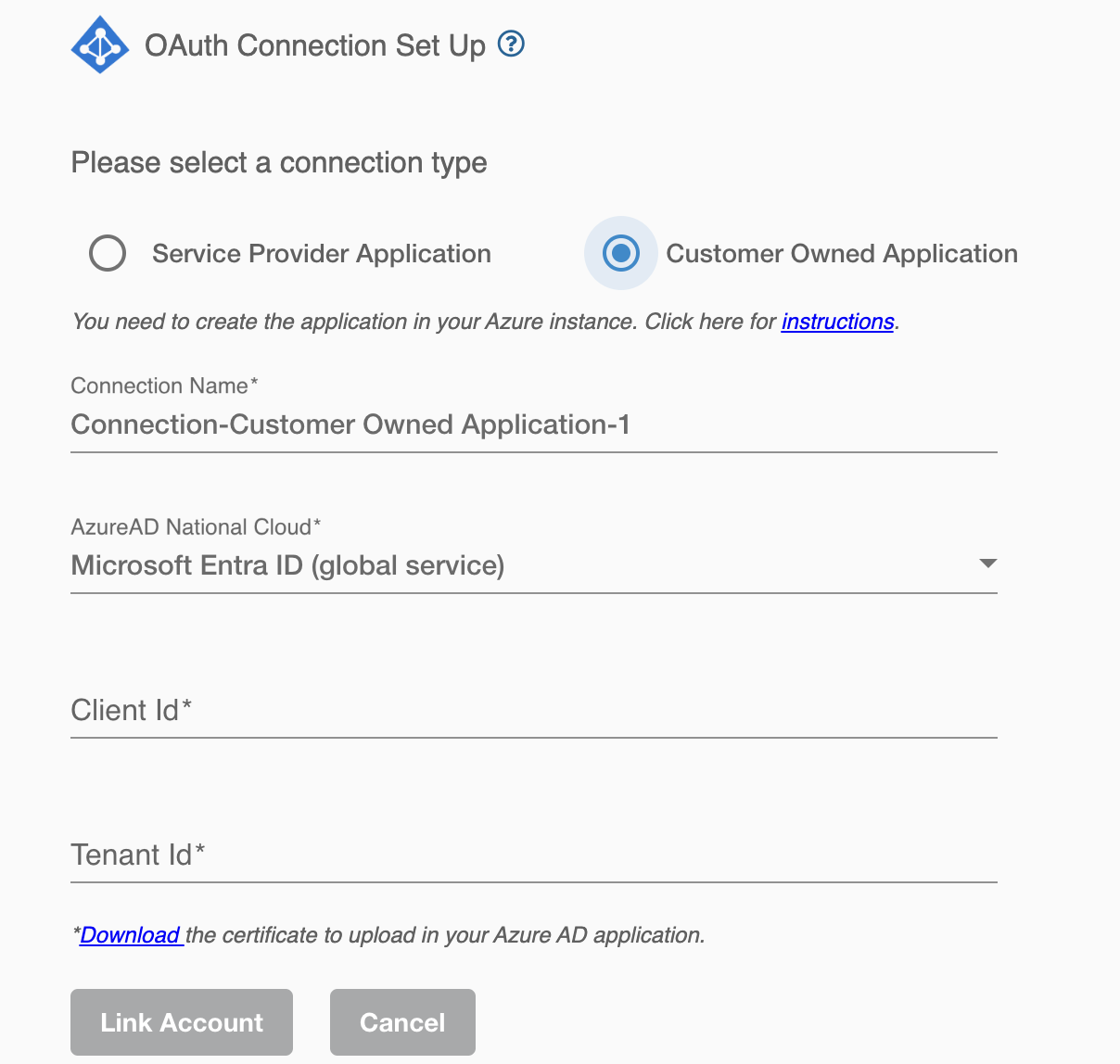
Customer Owned Application¶
Hire2Retire does not require the user to sign-in for this connection. Instead, for automation purposes, it will use your application service principal as a service account. Choosing this connection requires you to manage your service account's Application Permission in your Azure AD instance.
Create a Connection¶
You need to have application registered on your tenant & provide necessary permission required by Hire2Retire. Hire2Retire requires the following details to create a connection.
- Azure National cloud - Select the specific national or regional instance of a cloud service, such as Microsoft Azure National Cloud, tailored to meet local regulatory and compliance needs.
- Client ID - Application ID
- Tenant ID - Unique identifier of the Azure AD instance.
Navigate to the "Overview" blade within your registered application to locate both the Tenant ID and the Client/Application ID.
| Azure National cloud | Explanation |
|---|---|
| Microsoft Azure AD (global service) | A cloud-based identity and access management (IAM) service for managing who can access what in Microsoft cloud services (Azure, Office 365, etc.). Global: Not specific to any region or government, providing unified management across various clouds. |
| Microsoft Graph for US Government L4 | An API for accessing Microsoft 365 data in the Azure US Government cloud specifically for Impact Level 4 (L4) environments. |
| Microsoft Graph for US Government L5 (DOD) | Similar to L4, but for Impact Level 5 (L5) environments in the US Government cloud. |
| Microsoft Entra China operated by 21Vianet | A separate Azure environment and Microsoft Azure AD instance dedicated to China, operated by a local partner (21Vianet). |
To cred the application in your instance, follow the instructions below.
Application Registrations¶
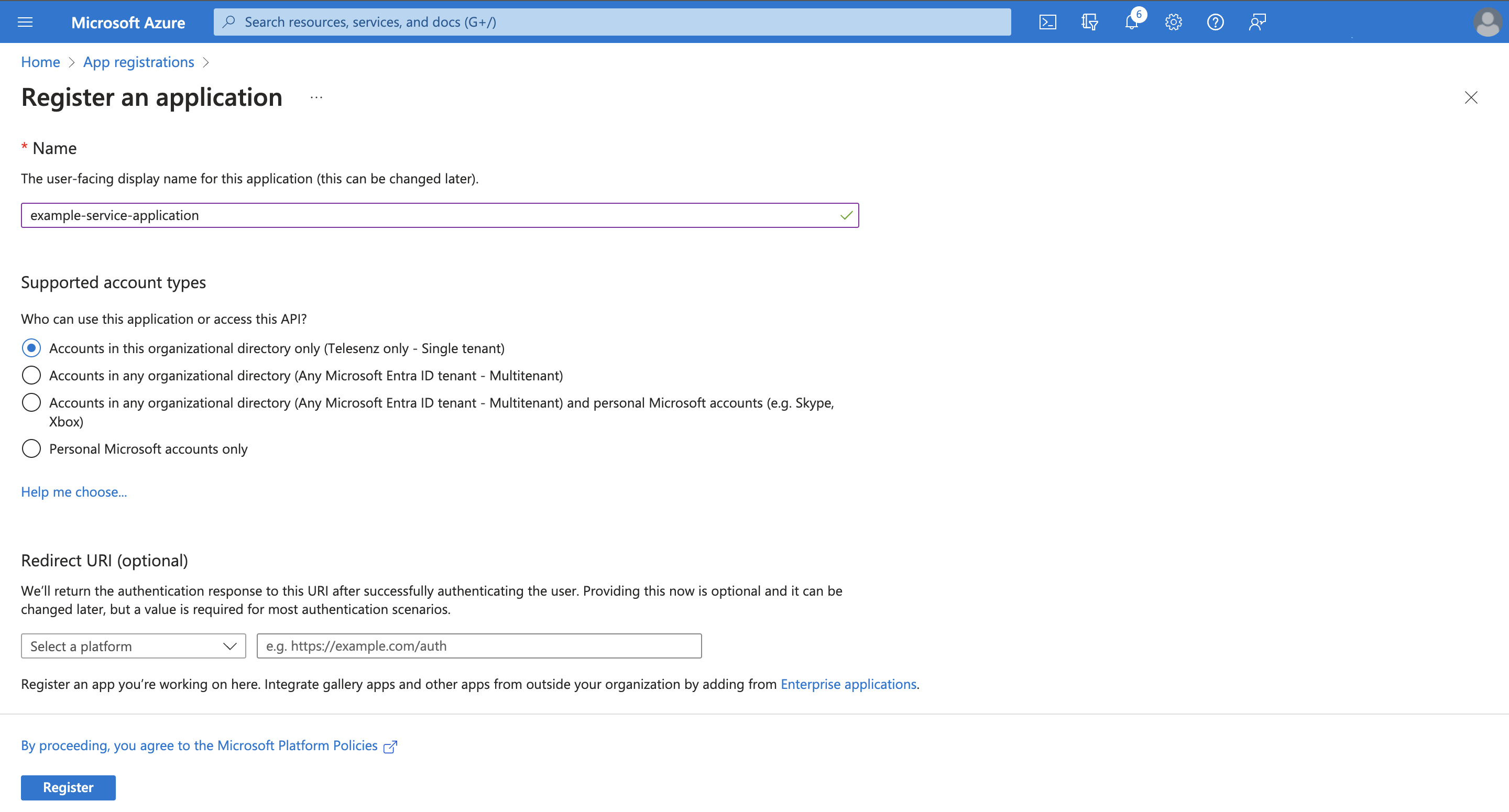
- Sign in to the Azure portal
- Browse to
App registrationsand selectNew registration. - Enter a display name for your application & leave Redirect URI (optional) field as blank.
- Specify who can use the application, we recommend to use single tenant if you are creating service account for Hire2Retire.
- Select Register to complete the initial app registration.
Credentials¶
Credentials enable your application to authenticate independently, elminating the need for user interaction during runtime. As a confidential client application, Hire2Retire will utilize these credentials to authenticate itself for automated tasks.
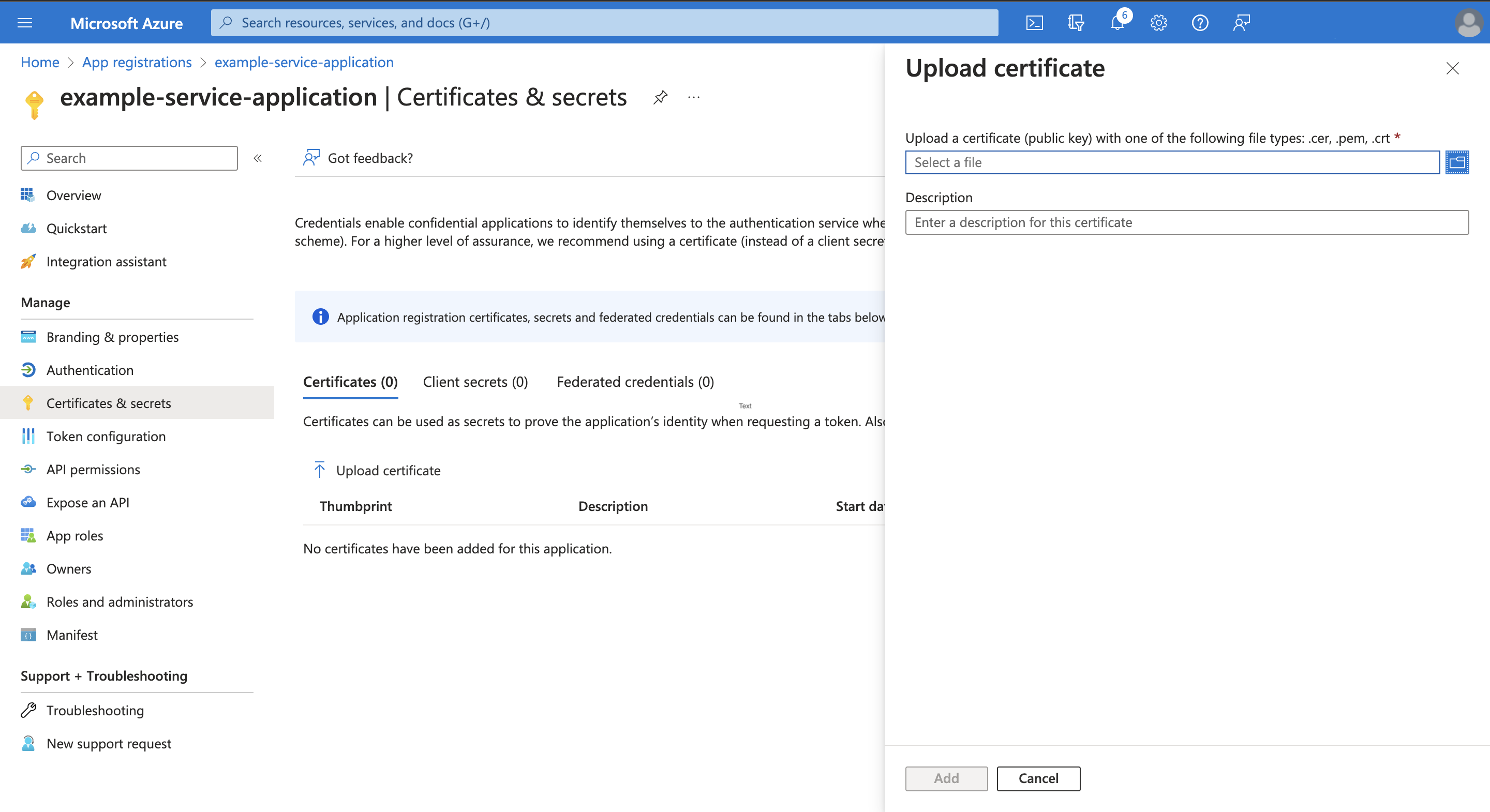
Follow the steps below to add credentials:
- Download the certificate from the Hire2Retire connection UI.
- In your registered application, select
Certificates & secrets>Certificates>Upload certificate - upload the downloaded certificate.
Certificates are the preferred credential type due to their enhanced security compared to client secrets.
This registered application can now be used as a service account for automation. To configure your Azure AD connection, click Link Account.
Application Permission¶
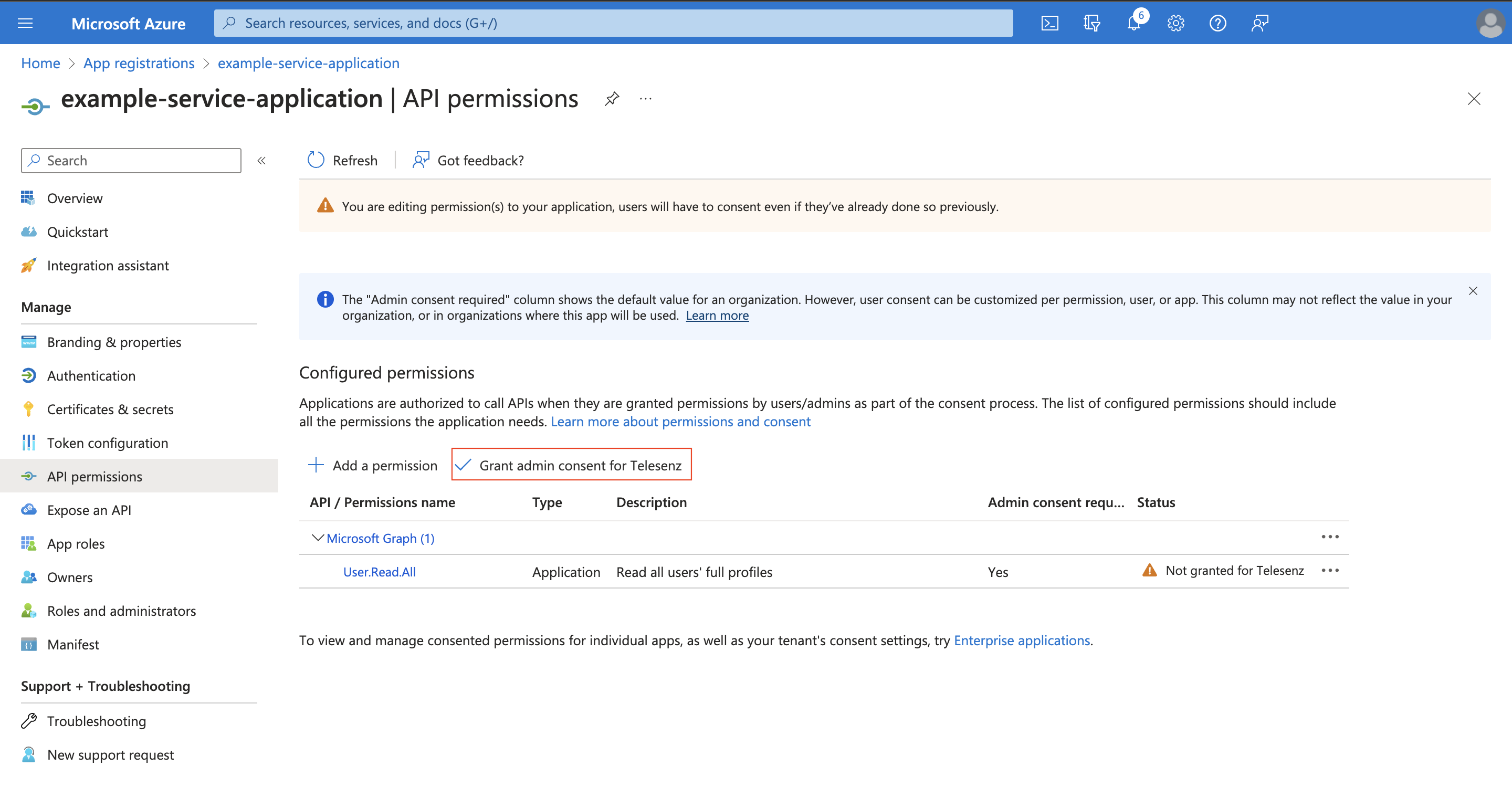
Set up application permissions for any application that needs to authenticate itself without the user's help or consent. To authorize a registered application to access the Microsoft Graph API, navigate to API permissions > Add a permission > Microsoft APIs > Microsoft Graph > Application permissions.
RoboMQ needs the following permissions on your registered application to provide a seamless integration eperience:
| Scopes | Explanation |
|---|---|
| User.ReadWrite.All | Allows the user to read and update the user profiles without a signed in user. |
| Group.ReadWrite.All | Allows the app to create groups, read all group properties and memberships, update group properties and memberships, and delete groups. Also allows the app to read and write conversations. All of these operations can be performed by the app without a signed-in user. |
| Directory.ReadWrite.All | Application requires this scope to reset their password. |
| User.EnableDisableAccount.All | Grants the ability to enable or disable any user account within the Azure AD tenant. |
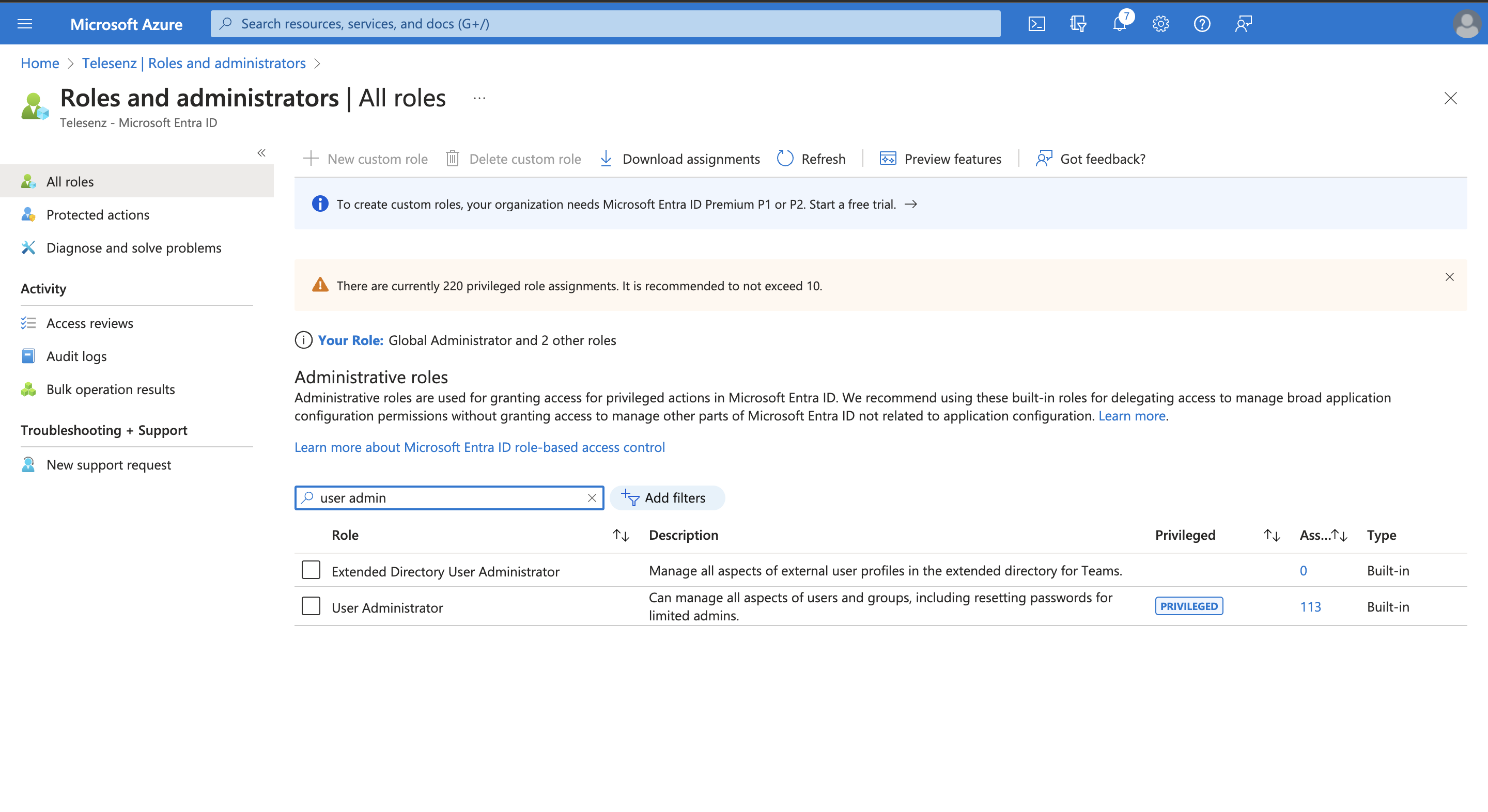
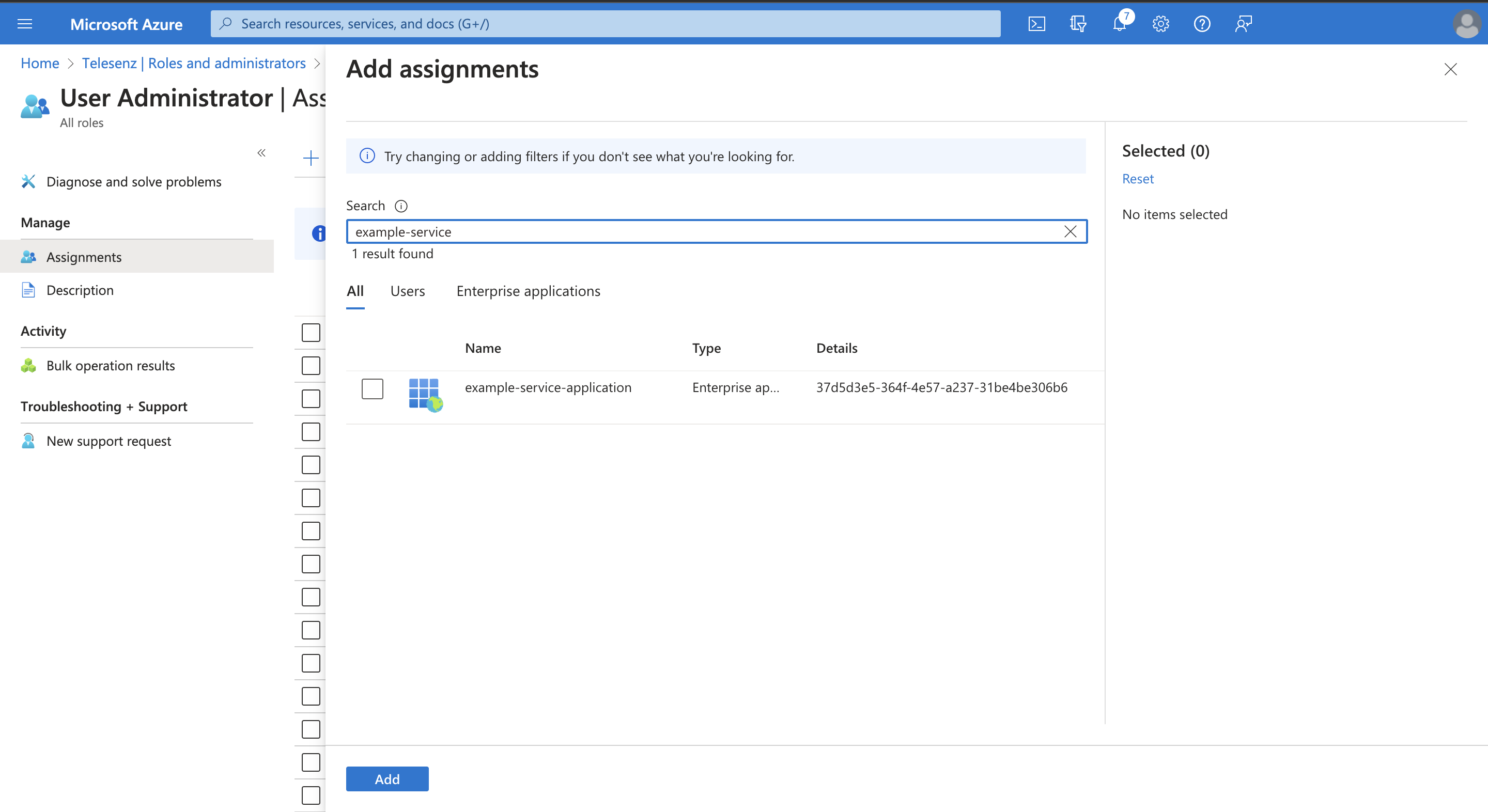
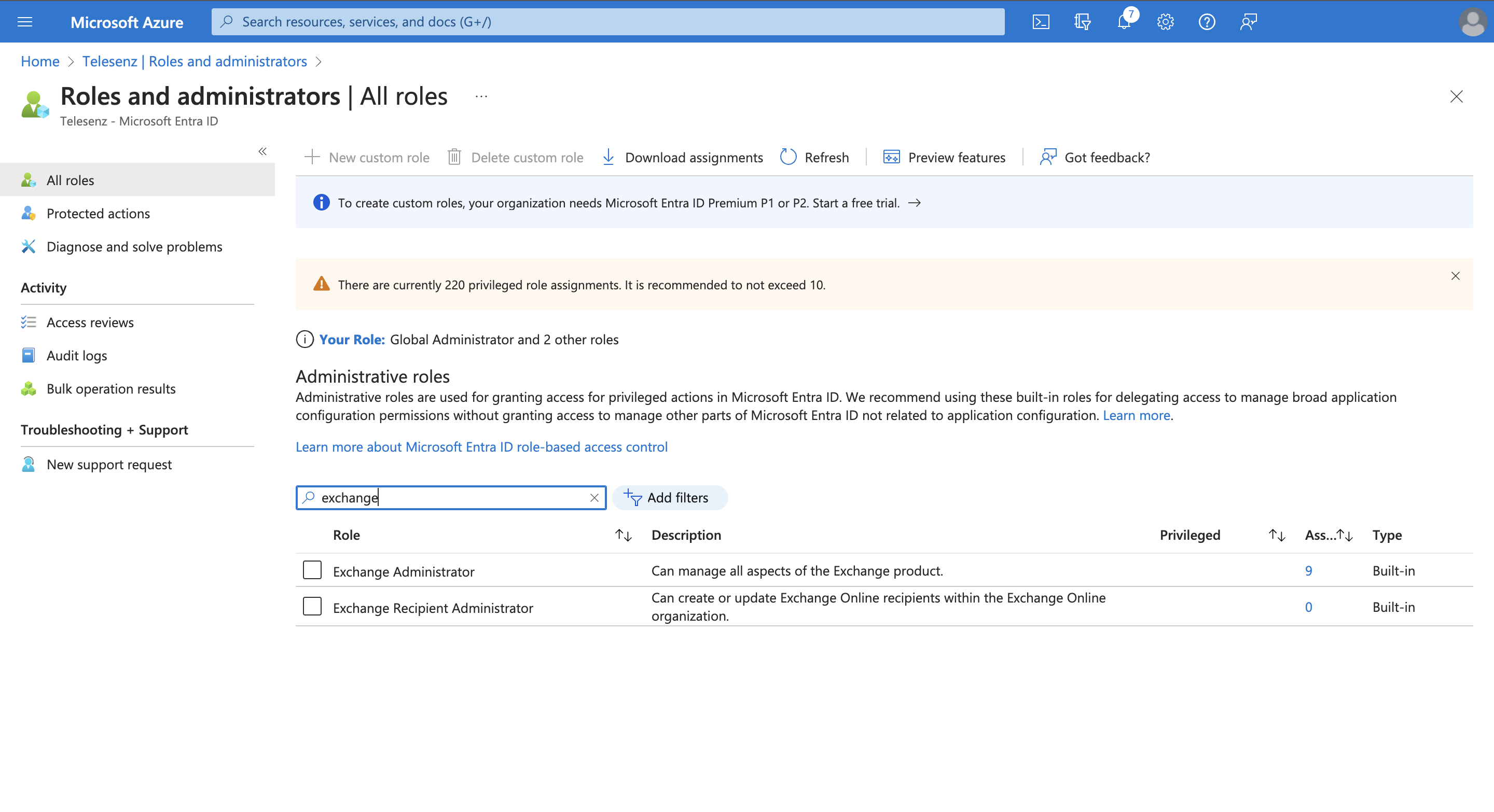
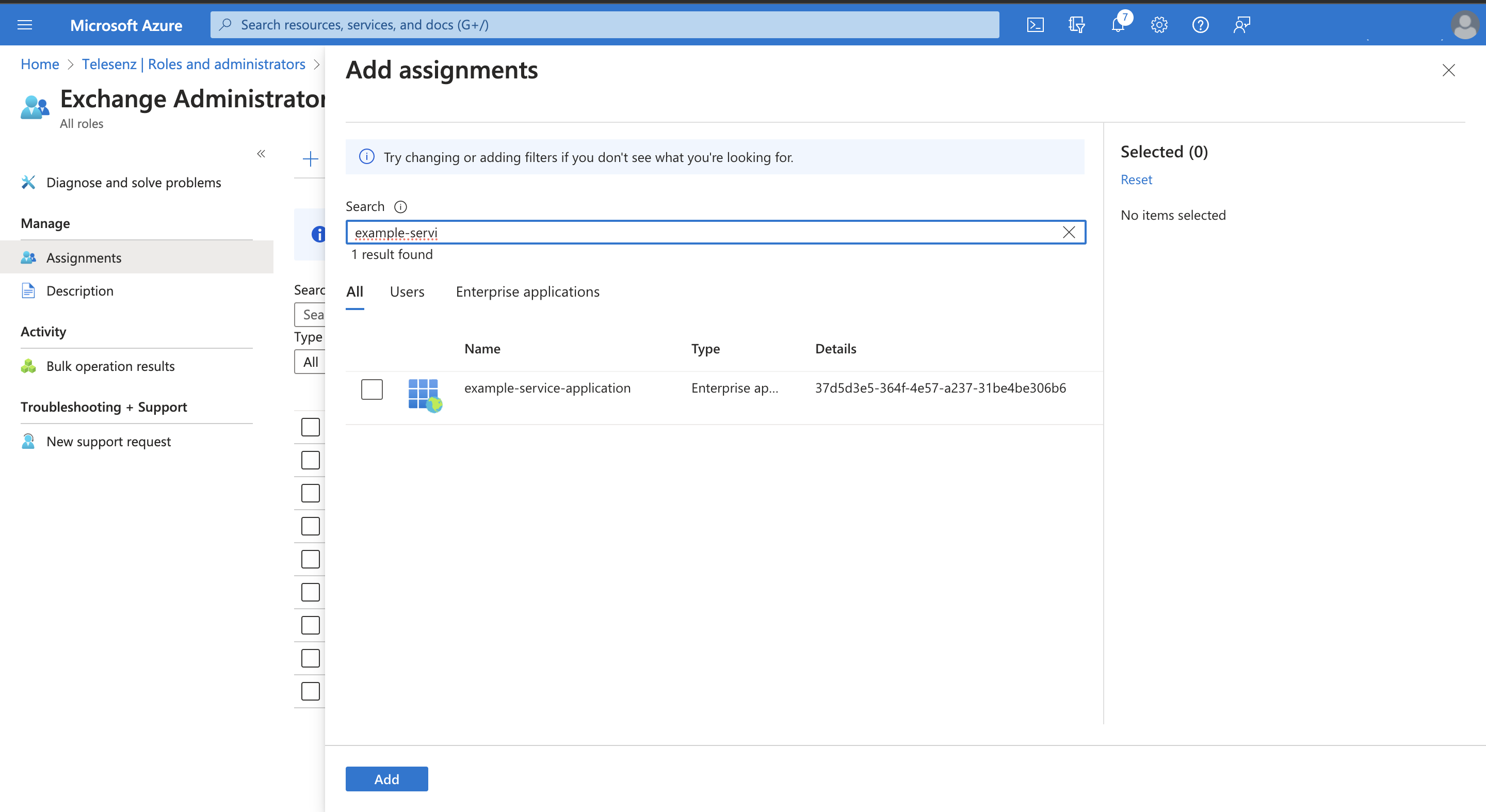
After giving the User.EnableDisableAccount.All permission, you will be required to give your application a User Administrator role by navigating to Microsoft Azure AD > Roles and administrators and search for user administrator, then Add assignments and search for your application name.
If you want to use exchange online feature, you need to add below permission.
Navigate to API permissions > Add a permission > APIs my organization uses and search for "office 365 exchange online" > Application permissions > Exchange
| Scopes | Explanation |
|---|---|
| Exchange.ManageAsApp | Allows the app to manage the organization's Exchange environment without any user interaction. This includes mailboxes, groups, and other configuration objects. To enable management actions, an admin must assign the appropriate roles directly to the app. |
After giving the Exchange.ManageAsApp permission, you will be required to give your application a Exchange Administrator role by navigating to Microsoft Azure AD > Roles and administrators and search for Exchange administrator, then Add assignments and search for your application name.
Grant admin consent to the permissions configured for the application.