Connection¶
Keycloak on Hire2Retire supports OAuth Client Credentials
The Client Credentials Flow involves an application exchanging its application credentials, such as client ID and client secret, for an access token.
We at RoboMQ pay utmost attention to keep your account secure. See our Security and Privacy Policies to learn more about how RoboMQ handles your account access.
| Object | Permission |
|---|---|
| User | Can Provision and Deprovision Users |
Client Credentials in Keycloak¶
Login to Admin Console and select Clients tab. From here you can create new client or use existing client admin-cli to get Client Id and Client Secret.
Configure the admin-cli client:
-
Select
admin-cliclient from clients tab.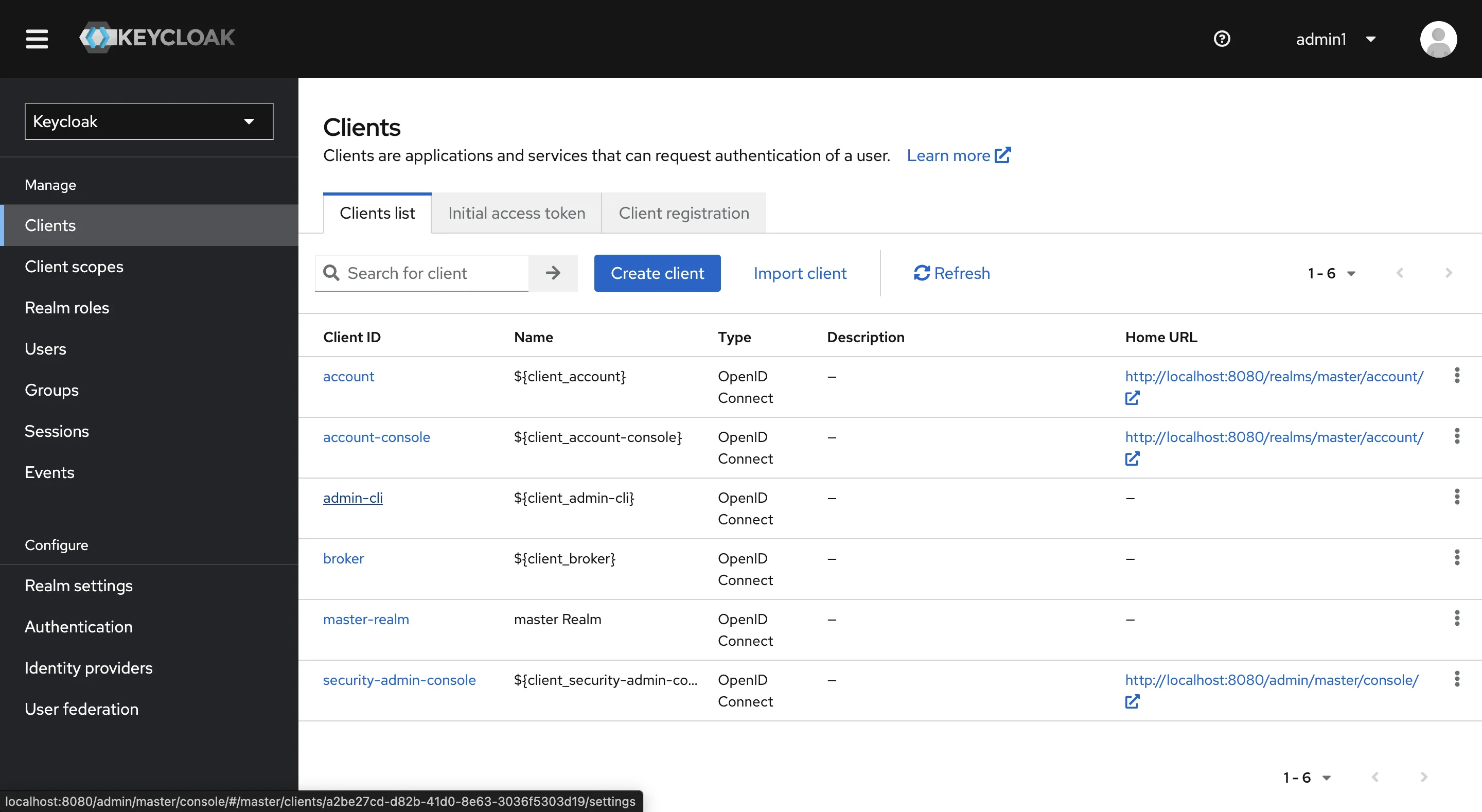 Figure 1. Keycloak Clients
Figure 1. Keycloak Clients -
Configure the client:
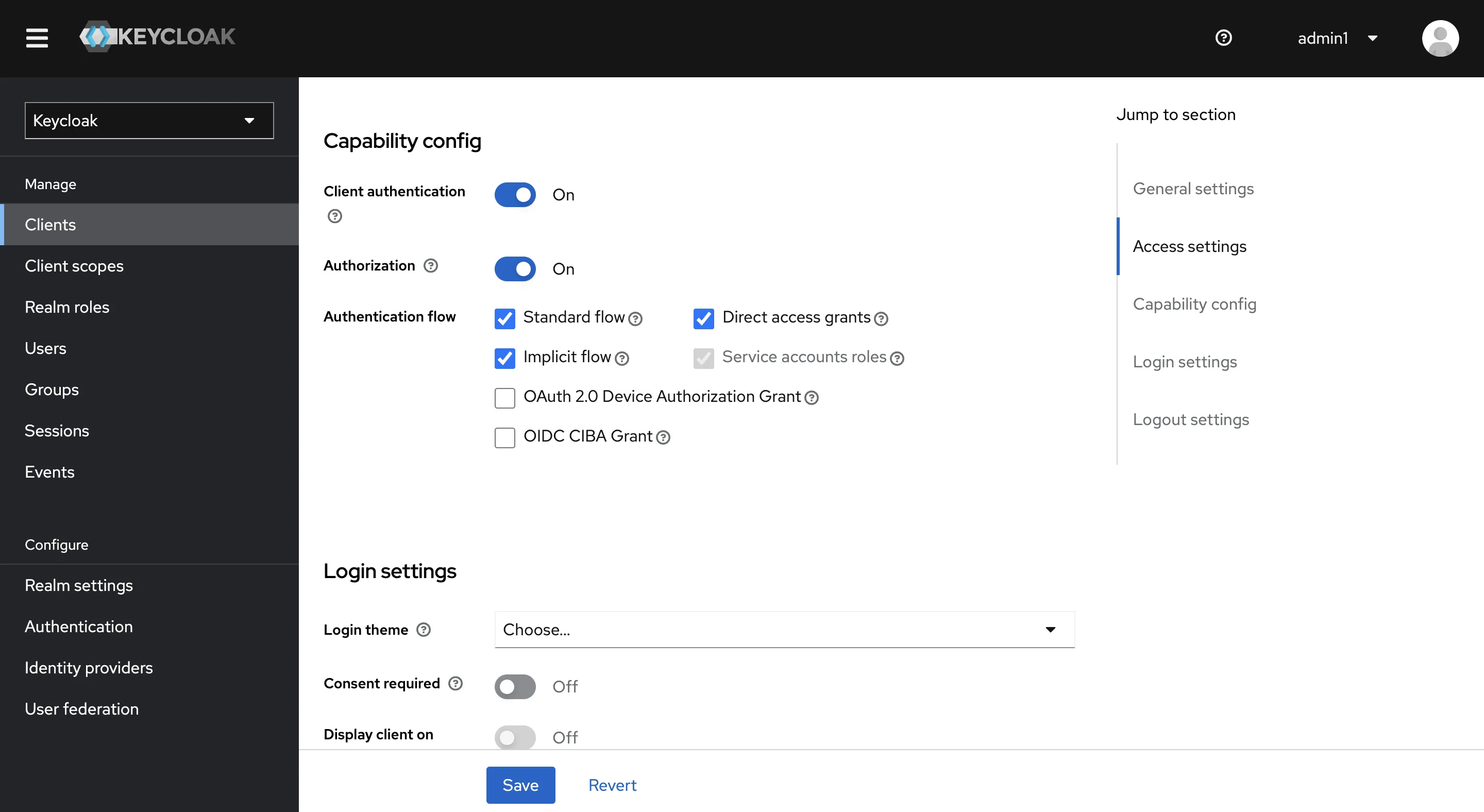 Figure 2. Keycloak Client Configuration
Figure 2. Keycloak Client ConfigurationClick on
Savebutton. -
Go to
Service Account Rolestab and assignadmin-roleto client.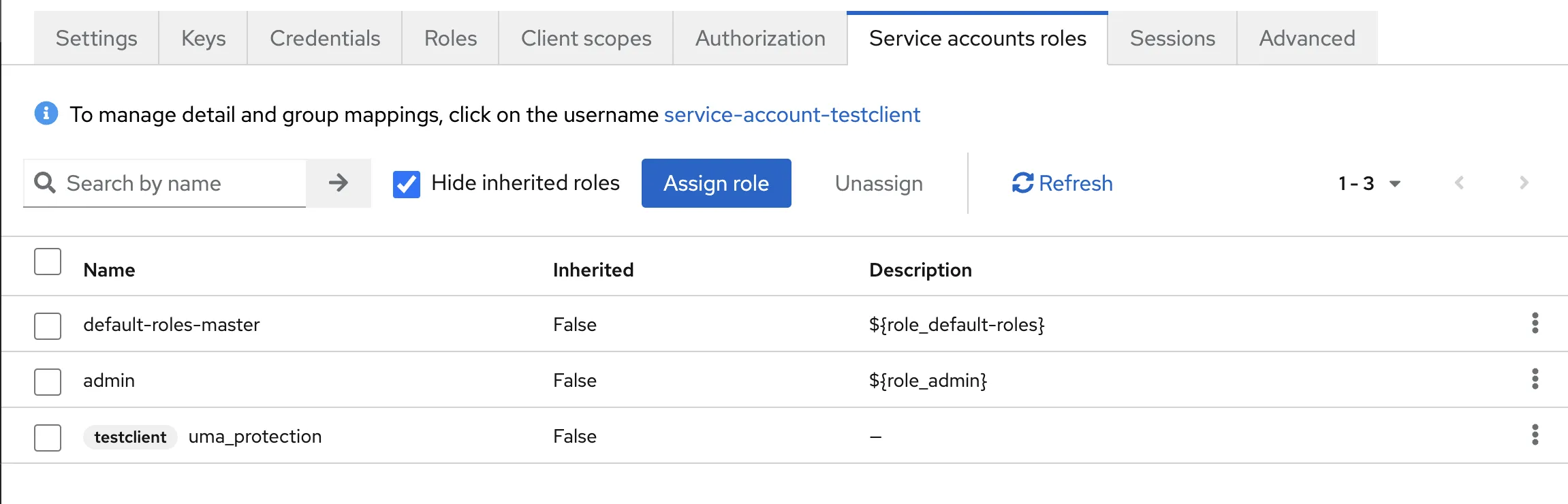 Figure 3. Keycloak Service Account Roles
Figure 3. Keycloak Service Account Roles -
Now, Client Secret can be obtained from
Credentialstab of client and Client ID is Client name(admin-cli).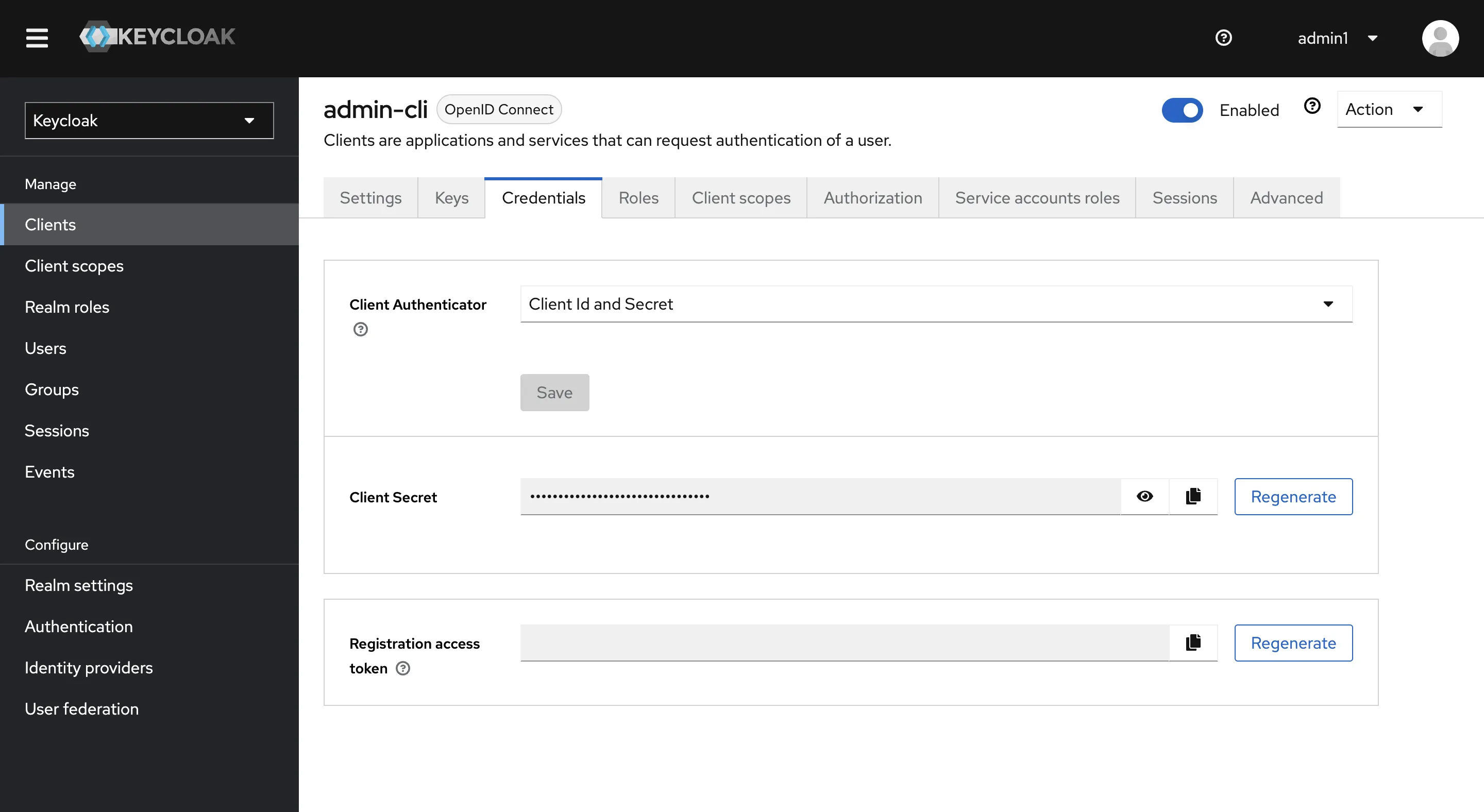 Figure 4. Keycloak Client ID and Client Secret
Figure 4. Keycloak Client ID and Client Secret
Link Keycloak account on Hire2Retire¶
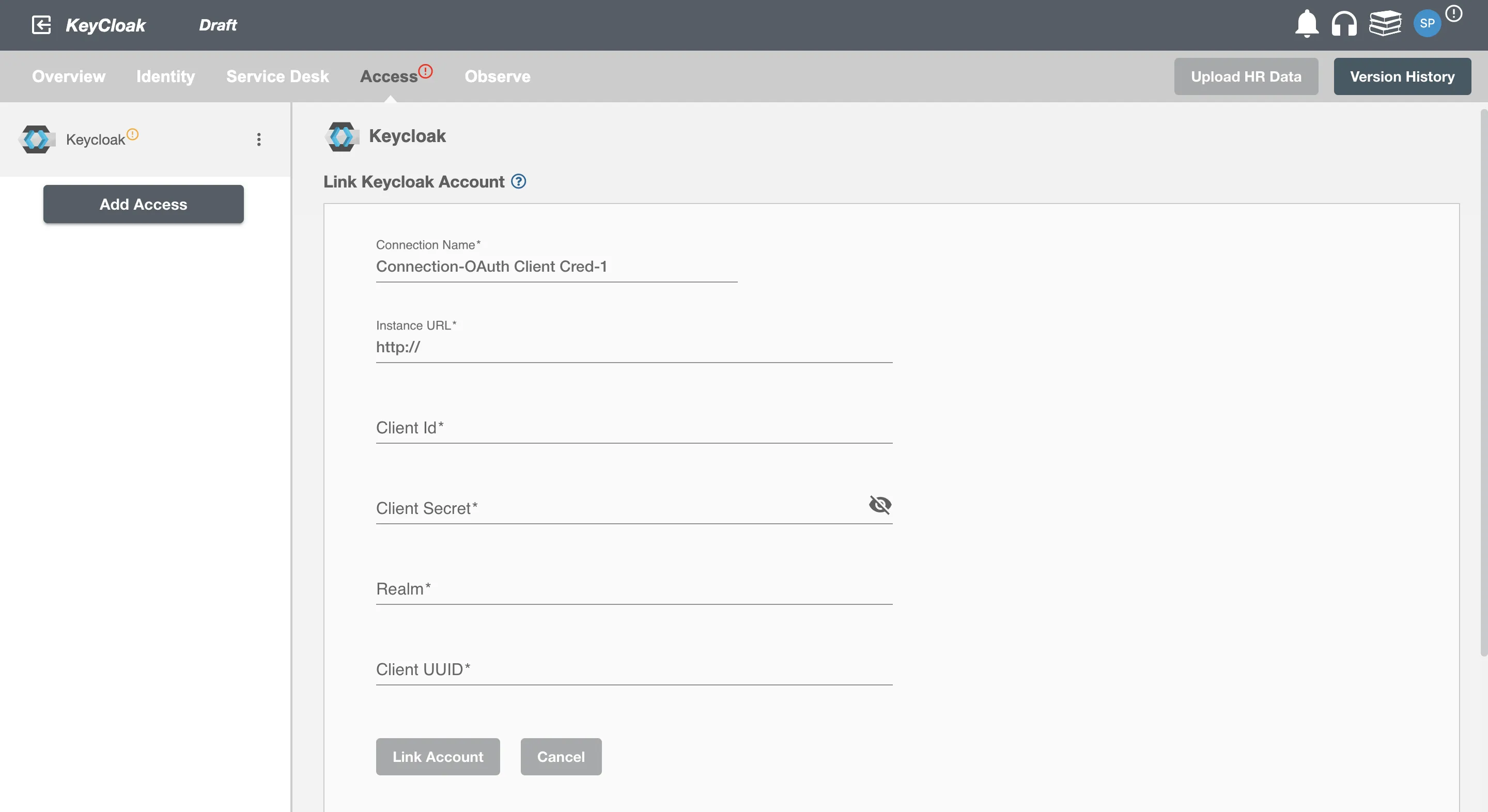
To establish a connection to the Keycloak on Hire2Retire Provisioning, you need to provide the following OAuth information:
-
Instance Url - Keycloak Account Instance Url.
-
Client Id - Client Id is the name of client.
-
Client Secret - The client secret is a confidential and unique identifier associated with your application when you register it as a client with the Keycloak platform.
-
Realm - Realm name.
-
Client UUID - Client UUID can be obtained from URL of the client
/clients/{client uuid}/
Once the connection is established successfully, then you can define the roles and mapping on Hire2Retire Provisioning.