Hybrid with SharePoint Online¶
By linking your Hybrid and SharePoint Online account with Hire2Retire, you can authorize RoboMQ to have a delegated access on your behalf to both applications. Hire2Retire needs the following permissions on your account to provide a seamless integration experience:
Create a Connection¶
Hybrid Connection¶
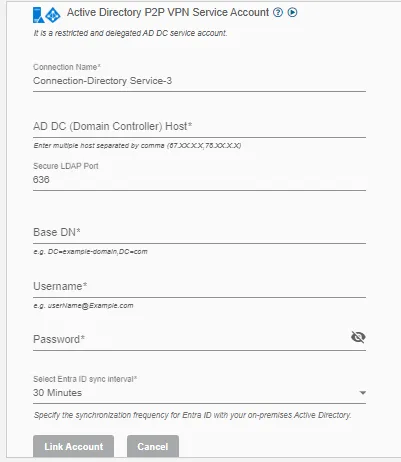
Hire2Retire requires the following details to create a connection.
- Connection Name - A user defined nomenclature for your connection. By default, the connect name is "Connection-Directory Service", you can change the name as per your preferences.
- Host - The host name is the IP address of your Active Directory Server. User can add more then one host for the same account by adding comma seperated values.
- Port - The TCP/IP port on which the Active Directory server is listening. Hire2Retire will only establish the LDAP connection with your SSL port. (The default is 636)
- Base DN - It is a collection of objects that Hire2Retire will access within an Active Directory network. An object can be a single user, a group of users or a hardware component, such as a computer or printer. Each base DN holds a database containing object identity information. It should be given in the format "DC=example-domain,DC=com"
- Username - The username to access the Active Directory server. Please make sure it belongs to the security group "Domain Admin" and has delegated control to target Organization Units (OU).
- Password - The Password to access the Active Directory server.
SharePoint Online Connection¶
To establish SharePoint Online connection, you need to have an application registered on your tenant with required permissions. You can either register a new application or use an existing application and add the required permissions.
Hire2Retire requires the following details to create a connection.
- Client Id - Entra ID Application's Unique Identifier.
- Tenant Id - Unique identifier of the Entra ID instance.
- SharePoint Online Admin Site URL - A unique web address used by SharePoint Online administrators to access the SharePoint Admin Center.
If you can't find these values, refer to our detailed guide.
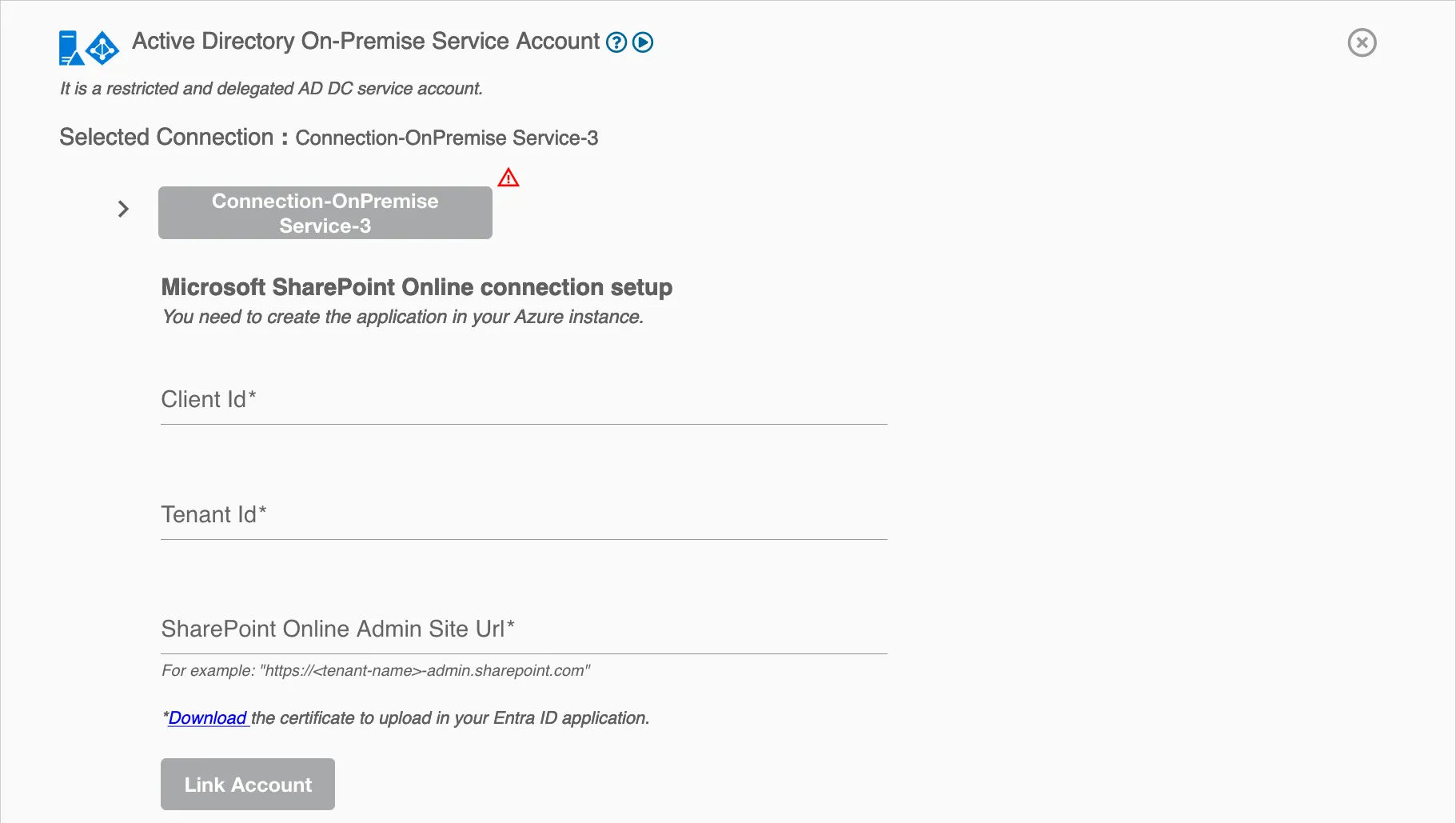
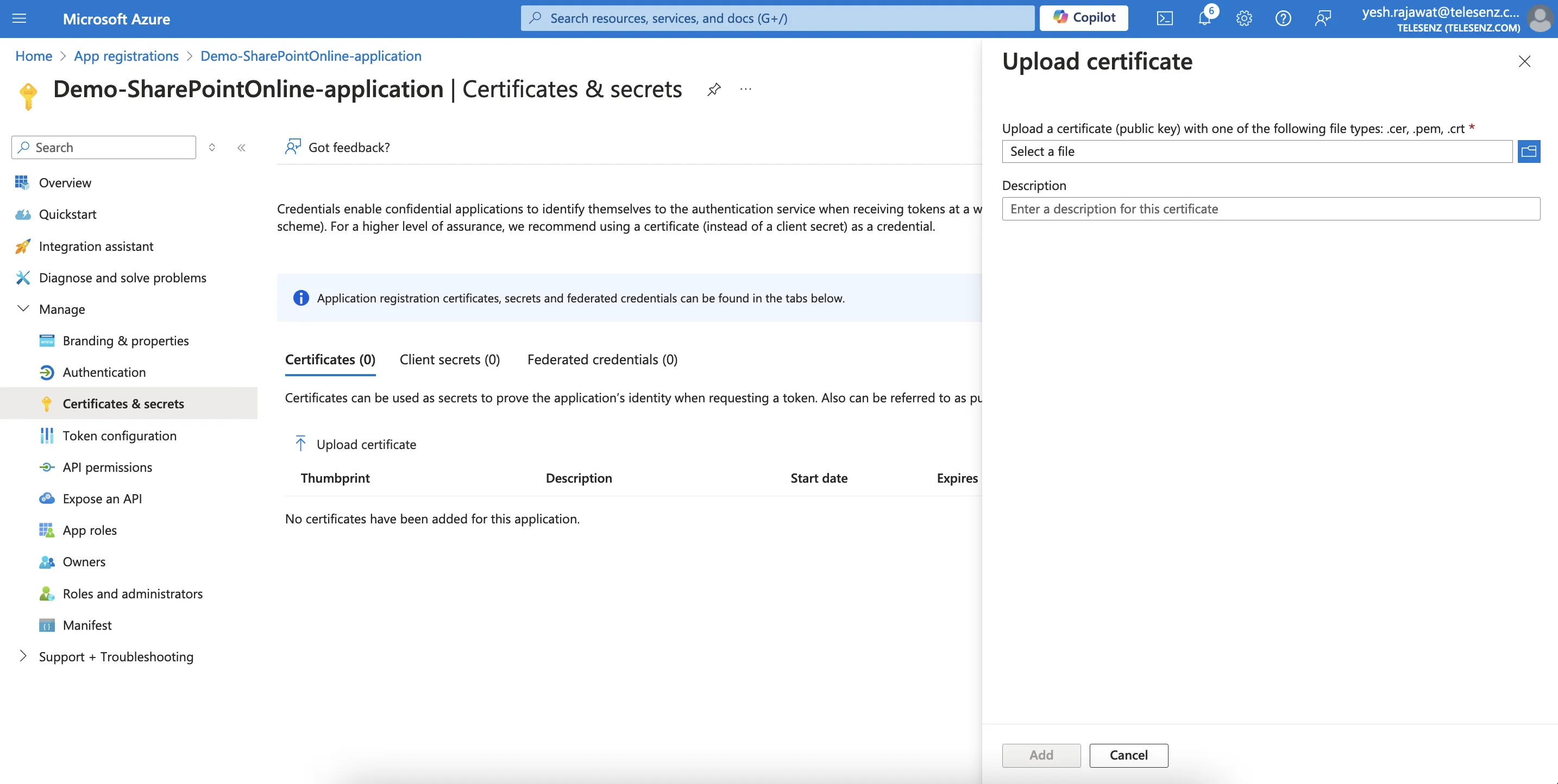
Certificate¶
Certificates enable your application to authenticate independently, elminating the need for user interaction during runtime. As a confidential client application, Hire2Retire will utilize these certificates to authenticate itself for automated tasks.
Follow the steps below to upload the certificate:
- Download the certificate from the Hire2Retire connection UI.
- In your registered application, select
Certificates & secrets>Certificates>Upload certificate - Upload the certificate.
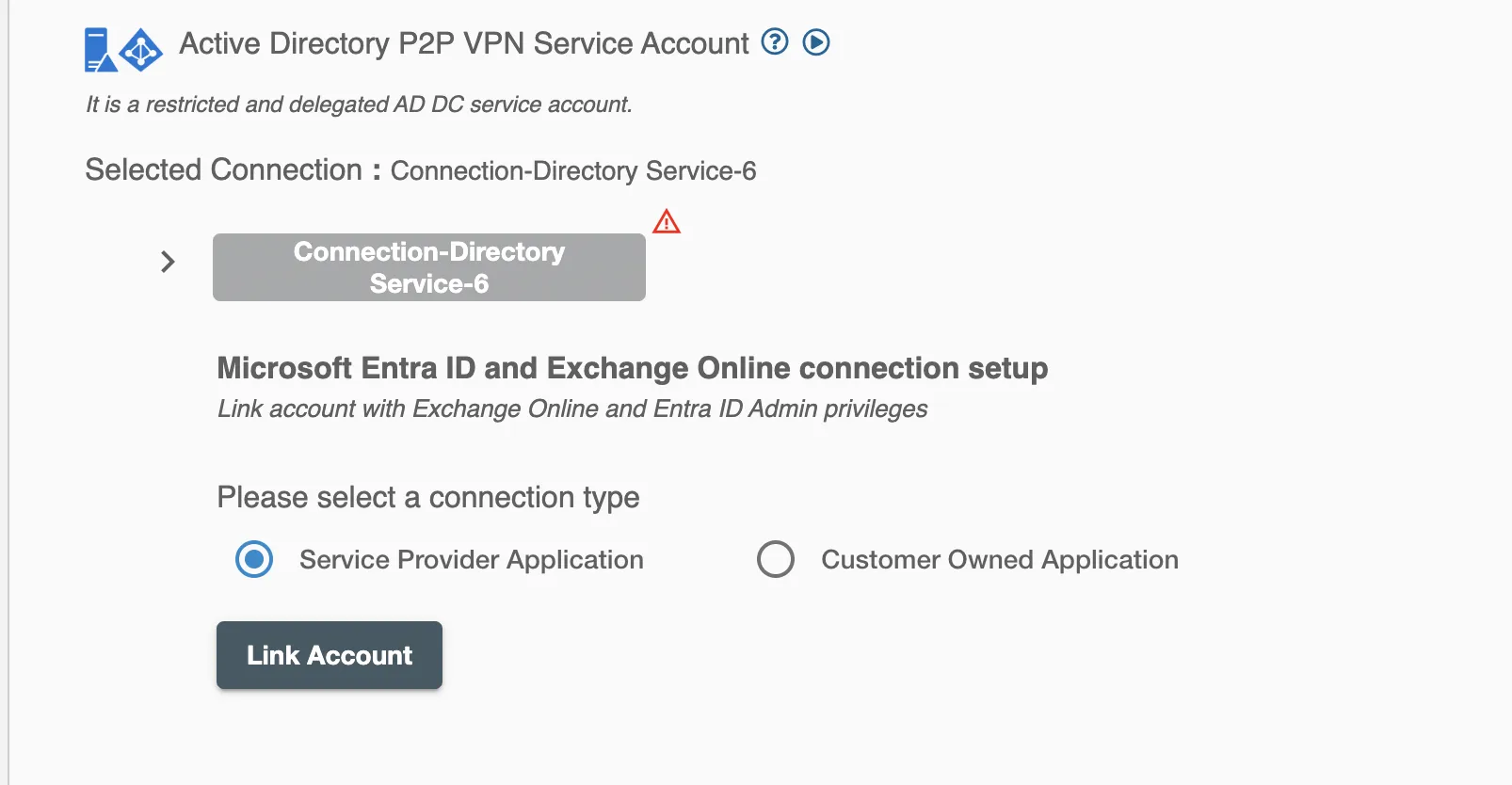
The Hire2Retire platform further provides two connection types for Hybrid applications:
- Service Provider Application - In this option, you'll be require to sign-up and delegating the accesses to the RoboMQ application on your behalf
- Customer Owned Application - This option is recommended if you prefer employing your registered application for automation purposes.
Service Provider Application¶
Hybrid application on hire2retire uses OAuth authorization. By linking your Hybrid account with hire2retire, you can authorise the RoboMQ application to have delegated access on your behalf, for which you will be provided with a consent window whenever new resource access permission is required by hire2retire. RoboMQ needs the following permissions on your account to provide a seamless integration experience:
| Scopes | Explanation |
|---|---|
| User.ReadWrite.All | Read and write all user's full profiles |
| Group.ReadWrite.All | Read and write all groups |
| Directory.AccessAsUser.All | Application requires this scope to reset their password. |
| offline_access | Maintain access to data you have given it access to. When a user approves the offline_access scope, your app can receive refresh tokens from the Microsoft identity platform token endpoint. Refresh tokens are long-lived. Your app can get new access tokens as older ones expire. |
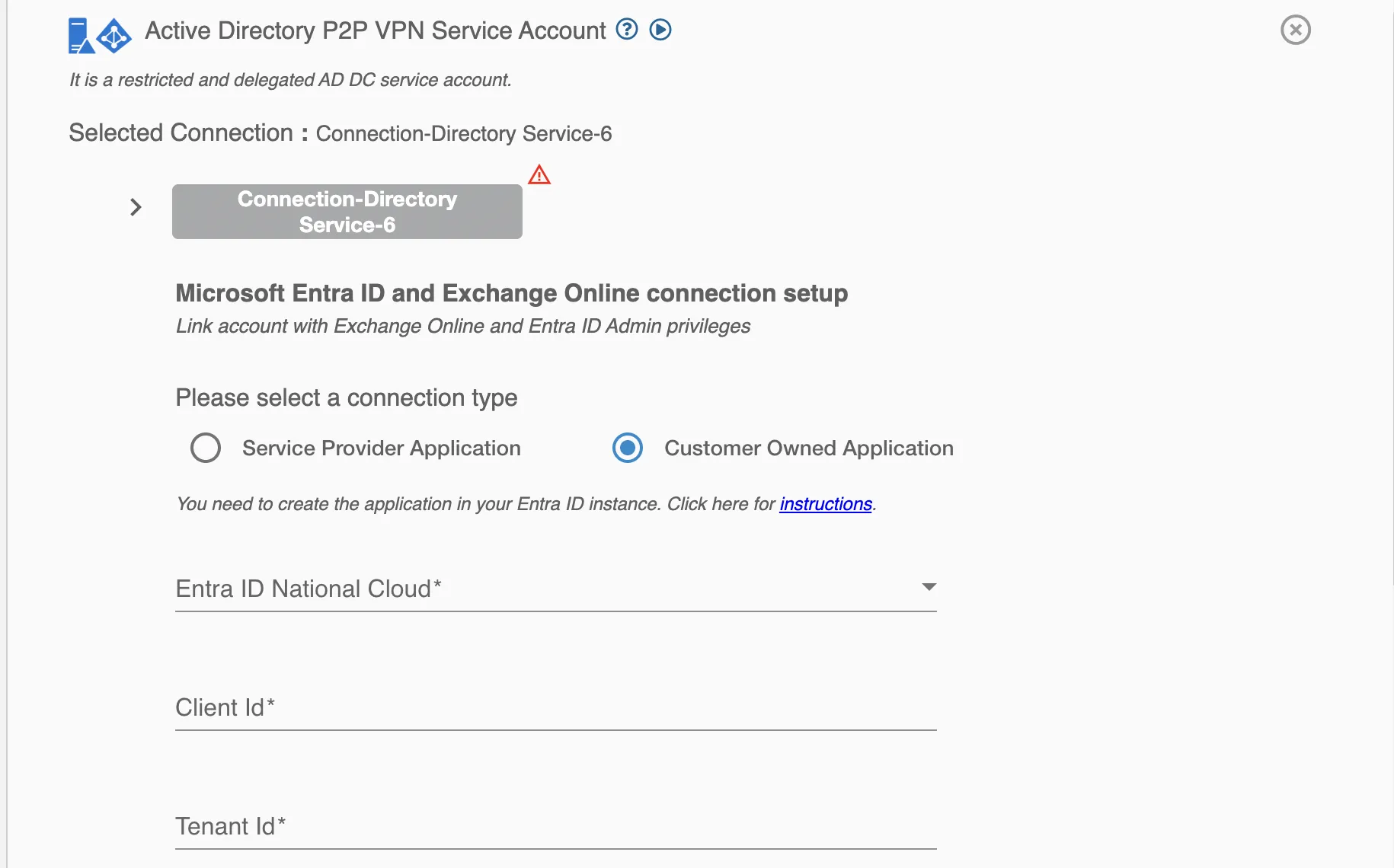
Customer Owned Application¶
Hire2Retire does not require the user to sign-in for this connection. Instead, for automation purposes, it will use your application service principal as a service account. Choosing this connection requires you to manage your service account's Application Permission in your Hybrid instance.
Create a Connection¶
You need to have application registered on your tenant & provide necessary permission required by Hire2Retire. Hire2Retire requires the following details to create a connection.
- Entra ID National cloud - Select the specific national or regional instance of a cloud service, such as Microsoft Entra ID National Cloud, tailored to meet local regulatory and compliance needs.
- Client ID - Application ID
- Tenant ID - Unique identifier of the Entra ID instance.
If you are configuring a connection with a multi-domain controller setup, you can provide host values for each domain controller in your AD along with their respective base DN and port. You can also provide comma separated list of IP/host addresses for each domain controller.
By checking the 'Use Global Catalog' checkbox, you can enable the Global Catalog (GC) for your Active Directory connection, which facilitates efficient searches for user and group information across multiple domains.
Application Permission¶
Set up application permissions for any application that needs to authenticate itself without the user's help or consent. To authorize a registered application to access the Microsoft Graph API, navigate to API permissions > Add a permission > Microsoft APIs > Microsoft Graph > Application permissions.
RoboMQ needs the following permissions on your registered application to provide a seamless integration eperience:
| Scopes | Explanation |
|---|---|
| User.ReadWrite.All | Allows the user to read and update the user profiles without a signed in user. |
| Group.ReadWrite.All | Allows the app to create groups, read all group properties and memberships, update group properties and memberships, and delete groups. Also allows the app to read and write conversations. All of these operations can be performed by the app without a signed-in user. |
| Directory.ReadWrite.All | Application requires this scope to reset their password. |
| User.EnableDisableAccount.All | Grants the ability to enable or disable any user account within the Entra ID tenant. |
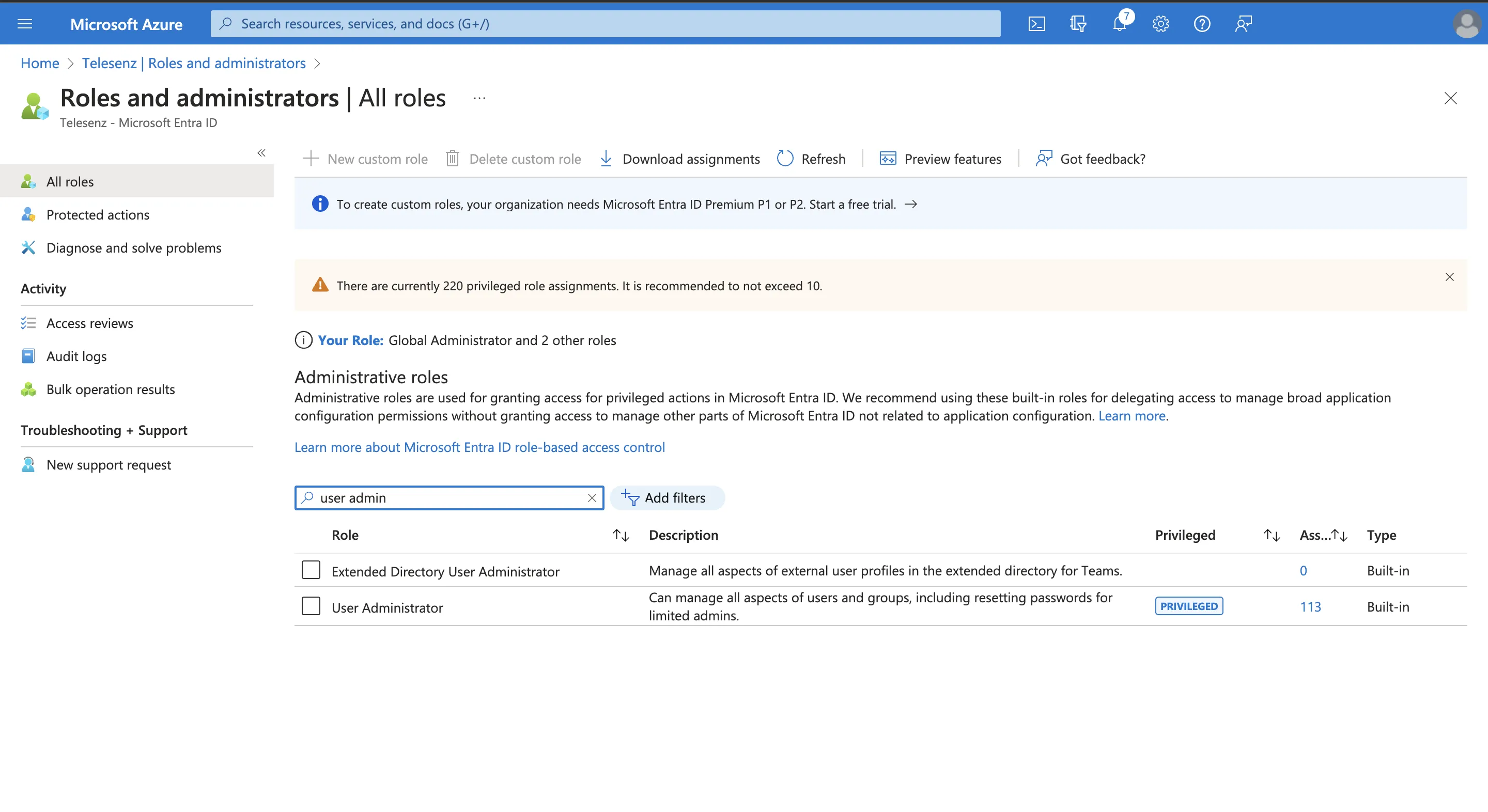
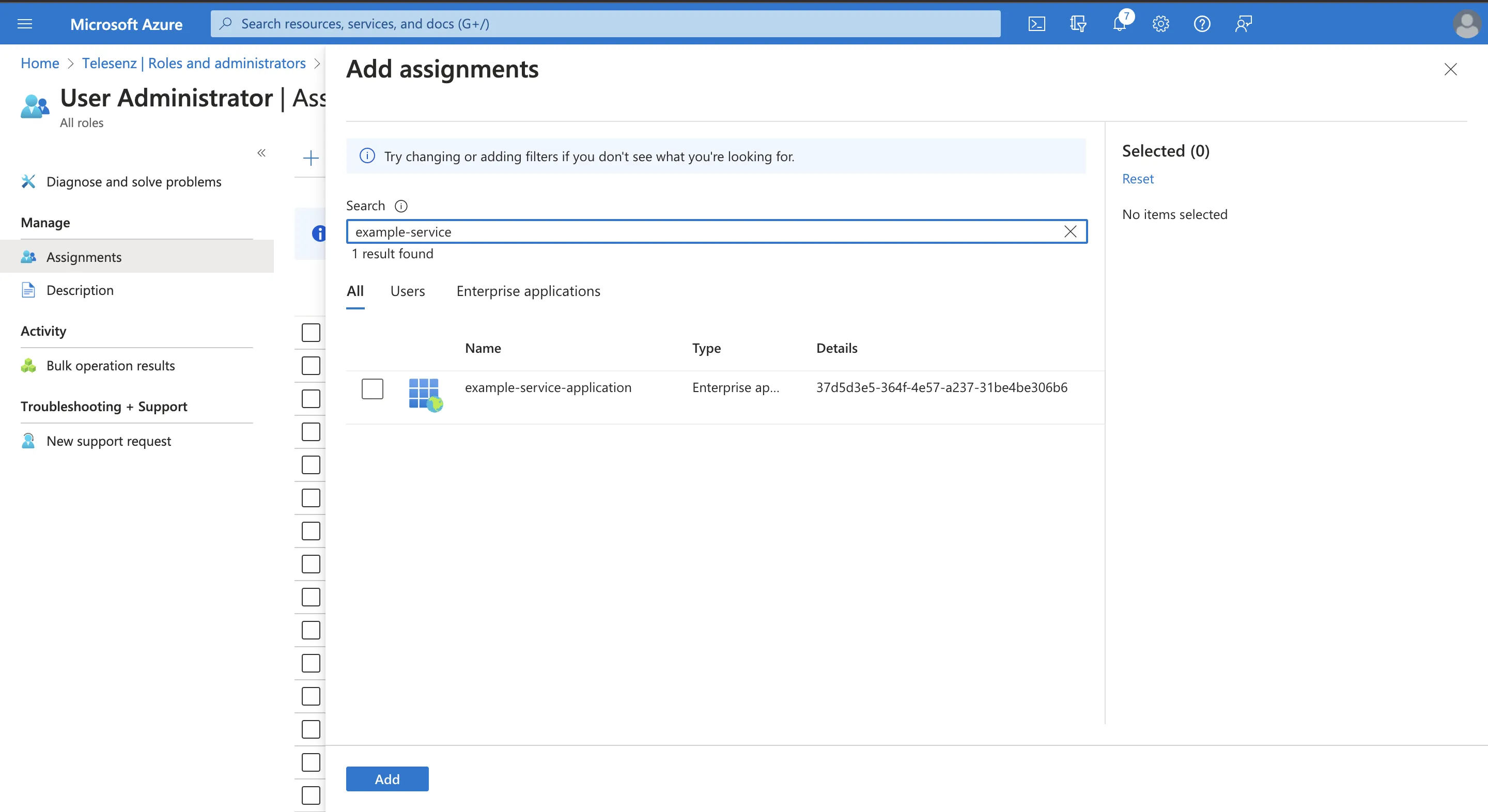
After giving the User.EnableDisableAccount.All permission, you will be required to give your application a User Administrator role by navigating to Microsoft Entra ID > Roles and administrators and search for user administrator, then Add assignments and search for your application name.